Hack Wi-Fi Password:KisMAC This is a latest OS in mac if you prefer the good graphic user interface (GUI) that is known as sniffer for wifi networks.However, if we install the right adapter we can find out some keys.All the detail is given in the video that is given below. Now, here are some steps that you can easily 'Hack WiFi Password using Kali Linux', So, Following steps will help wifi password. STEP1; First of all, Open the terminal window in Kali Linux. To open a terminal window in kali Linux use keyboard shortcut ctrl+alt+t, or type terminal in the search box.
- How To Hack Wifi Password On Mac Using Terminal 2019
- How To Hack Wifi Password On Mac Using Terminal 2020
To hack the wifi password with WEP/WPA2. This is done by following command on the terminal. This will trigger the router to reconnect/reauthenticate the chosen client. This is how the authentication process can be analyzed. On the terminal with airodump- ng running, a 'WPA handshake' message should appear. Recently posted Second Method to hack wifi password. How to Hack Wifi Password – First Method: First of all you need to scan for available wireless networks. You can use“NetStumbler” or “Kismet” for Windows and Linux and KisMacfor Mac. It’ll also show how the Wi-fi network is encrypted. The two most common encryption techniques are. Every new hacker loves to Google the words “How to hack WiFi passwords?” So i thought why not make a blog post on it. PS Every professional hacker was a script kiddie at some point. Before we start lets look at some terminology. BSSID- It is the MAC addrses of a device ESSID- It is the name of a device. AP- Access Point, example a router.

Every new hacker loves to Google the words “How to hack WiFi passwords?” So i thought why not make a blog post on it.
PS Every professional hacker was a script kiddie at some point
Before we start lets look at some terminology.
BSSID- It is the MAC addrses of a device
ESSID- It is the name of a device.
AP- Access Point, example a router.
There are a few types of WiFi encryption:
- WEP (Wired Equivalency Privacy)
- WPA(Wi-Fi Protected Access)
- WPA2(Wi-Fi Protected Access 2)
- WPA2 with WPS(Wireless Protected Setup)
- WPA3(Wi-Fi Protected Access)
For this post we will only be focusing on WPA2 because that’s the one most commonly used.
WPA2 uses the Advanced Encryption Standard (AES) and Counter Mode with Cipher Block Chaining Message Authentication Code Protocol (CCMP), respectively.
Developed by the U.S. government to protect classified data, AES comprises three symmetric block ciphers. Each encrypts and decrypts data in blocks of 128 bits using 128-bit, 192-bit and 256-bit keys. Although the use of AES requires more computing power from APs and clients, ongoing improvements in computer and network hardware have mitigated performance concerns.
CCMP protects data confidentiality by allowing only authorized network users to receive data, and it uses cipher block chaining message authentication code to ensure message integrity.
WPA2 also introduced more seamless roaming, allowing clients to move from one AP to another on the same network without having to reauthenticate, using Pairwise Master Key caching or preauthentication.
WPA2 Password Hacking
Okay, so hacking WPA-2 PSK involves 2 main steps-
- Getting a handshake (it contains the hash of password, i.e. encrypted password)
- Cracking the hash.
What we need is:
- An attacker (you)
- A client
- An AP (Access point)
- A network adapter capable of packet injection. (i recommend ALFA AWUS036NH)
When the client and the AP communicate in order to authenticate the client, they have a 4 way handshake that we can capture. This handshake has the hash of the password. Now there’s no direct way of getting the password out of the hash, and thus hashing is a robust protection method. But there is one thing we can do. We can take all possible passwords that can exists, and convert them to hash. Then we’ll match the hash we created with the one that’s there in the handshake. Now if the hashes match, we know what plain text password gave rise to the hash, thus we know the password. If the process sounds really time consuming to you, then its because it is. WPA2 hacking (and hash cracking in general) is pretty resource intensive and time taking process. Now there are various different ways cracking of WPA2 can be done. But since WPA2 is a long shot, we shall first look at the process of capturing a handshake.
Now since i don’t want you to remain script kiddies forever, let me explain what the 4 way handshake actually is.
The Four-Way Handshake
The authentication process leaves two considerations: the access point (AP) still needs to authenticate itself to the client station (STA), and keys to encrypt the traffic need to be derived. The earlier EAP exchange or WPA2-PSK has provided the shared secret key PMK (Pairwise Master Key). This key is, however, designed to last the entire session and should be exposed as little as possible. Therefore the four-way handshake is used to establish another key called the PTK (Pairwise Transient Key). The PTK is generated by concatenating the following attributes: PMK, AP nonce (ANonce), STA nonce (SNonce), AP MAC address, and STA MAC address. The product is then put through PBKDF2-SHA1 as the cryptographic hash function.
The handshake also yields the GTK (Group Temporal Key), used to decrypt multicast and broadcast traffic.
The actual messages exchanged during the handshake are depicted in the figure and explained below:
Here is YouTube video for a better understanding.
The Aircrack-ng suite
Aircrack-ng is a complete suite of tools to assess WiFi network security.
It focuses on different areas of WiFi security:
- Monitoring: Packet capture and export of data to text files for further processing by third party tools
- Attacking: Replay attacks, deauthentication, fake access points and others via packet injection
- Testing: Checking WiFi cards and driver capabilities (capture and injection)
- Cracking: WEP and WPA PSK (WPA 1 and 2)
Here is a breakdown of tools that we would use:
- Airmon-ng (for initiating monitor mode)
- Airodump-ng (to capture the handshake)
- Aireplay-ng (to deauthenticate clients)
- Aircrack-ng (to brute force the password)
Step 1 Set your interface to monitor mode.
Monitor mode or RFMON (Radio Frequency Monitor) mode, enables a device with a wireless network interface controller to monitor all traffic received from the wireless network. Unlike promiscuous mode, which is also used for packet sniffing, RFMON mode enables packets to be captured without having to connect or link with an access point. RFMON mode only works with wireless networks, while promiscuous mode can be applied to both wired and wireless networks.
How To Hack Wifi Password On Mac Using Terminal 2019
Now wlan0 is for me, for you it could be wlan1 or wlan2 anything else, depending on you card. So select the interface carefully.
As you can see station mode is disabled and monitor mode is now enabled.
Step 2 Find your target.
Find you targets BSSID by this command:
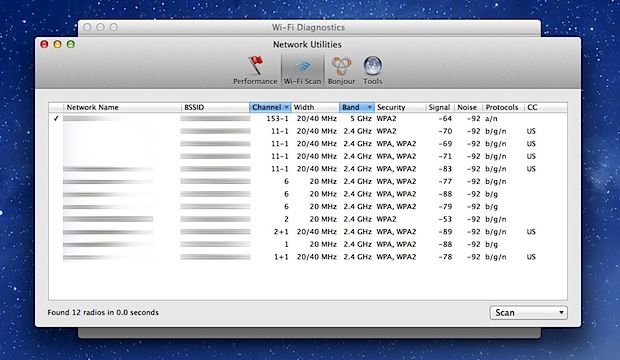
Yes i know there’s a lot of information over there, so lets break that down as well.
PWR: Signal strength
RXQ: Receive quality
Beacons: Number of announcement packets.
#Data: Number of captured packets
CH: Channel
ENC: Encryption Type
Cipher: Cipher type
Station: MAC address of the client.
Lost: Packets lost
Packets: Data packets sent by client
How To Hack Wifi Password On Mac Using Terminal 2020
Anyways, as you can see in the picture above, our target is called Test Router.
Step 3 Capture the Handshake
You will see something like this
The below area is to display clients connected to that AP. Now we need to simultaneously de-authenticate at least one client. In this case will de-authenticate 7A:AC:AD:CC:44:05.
So open another terminal
The command is
The -a is for the APs MAC address, the -c is for the clients MAC and -0 is for deauth mode.
After a few seconds press CTRL-Z to stop sending deauth packets. As soon as the client connects back, we would capture the hashed handshake file.
You can see on the top right corner that we captured the handshake file.
Step 4 Brute Forcing the handshake file
I have put the actual password in the file dic.txt along with some other random passwords. So we run aircrack-ng with the dictionary as well as the handshake file (.cap)
Now depending on your dictionary this can take a second or even weeks. I cracked it in a second because the dictionary was small and it contained the password.
Now you may be thinking that this isn’t the most efficient way of getting someones password.
Well the purpose of this article was to explain the basic attack vector used to hack WiFi passwords and to introduce you to the Aircrack-ng. If you want someones password, just go ask them.
There is another way we could get an APs (with WPA2) password and that is by exploiting the WPS pin vulnerability, we could get the password in just a few hours guaranteed, apparently that only works on old routers. So when i get a hold of one i’ll cover that topic as well.
Every type of WiFi encryption has its set vulnerabilities, for example the WEP has an issue with the implementation of the RC4 encryption algorithm. So stay tuned as i cover them one by one.
HAPPY HACKING
In this hi-tech life, we always need a working internet connection to manage both our professional and personal life. The most comfortable way to access internet everywhere anytime is by buying mobile data recharges but they are very expensive. Another good way to connect to free WiFi if it’s luckily available at your workplace, college or home. But everyone is not that lucky.
Everybody might have many fast WiFi hotspots available in their smartphone’s range, but they don’t have access to those WiFi connections because they are password protected and you don’t have access to them so, you can’t use those WiFi hotspot to access internet in your smartphone or laptop. But, what if you can hack a WiFi?
Yes, I am not joking. What if you can hack any WiFi available in your range and crack it’s password to access free and unlimited internet? IMO, if you can learn a way to hack a WiFi network then you can access free internet everywhere. Right?
So, I am telling you the method to hack a secured WiFi network, crack its password and enjoy free internet using it.
Before moving directly to the methods to hack WiFi networks lets first see what type of security and authentication methods are implemented in WiFi networks.
WiFi Security & Encryption Methods
- Open – This is WiFi networks with no authentication. Anyone in the WiFi range can connect his device to the network without any password in enjoy free internet. However, these networks are rarely available and also risky.
- WEP – Wired Equivalent Privacy (WEP) is a security protocol, specified in the IEEE Wireless Fidelity (Wi-Fi) standard, 802.11b, that is designed to provide a wireless local area network (WLAN) with a level of security and privacy comparable to what is usually expected of a wired LAN.
- WPA – WiFi Protected Access (WPA) is improved and more secured security protocol which arrived with lots of improvements in encryption and authentication methods of WEP.
- WPA2 PSK – It is short of Wi-Fi Protected Access 2 – Pre-Shared Key which is the latest and most powerful encryption method used in WiFi networks right now.
Hacking WiFi Networks with WEP, WPA and WPA2 PSK Security
As security features have been improved from WEP to WPA to WPA2 PSK WiFi authentication protocol, so obviously, WEP WiFi networks are very easy to hack compared to WPA and WPA2 PSK Security methods.
Almost every password-protected WiFi networks support both WPA/WPA2 PSK authentication. If somebody is already connected to the network, you can check in his network properties to see what encryption-type is being using by the targeted WiFi network.
But if you want to know encryption-type of WiFi network which is not connected to any device in your reach, you need Ubuntu operating system to do this.
In Ubuntu, you can use nmcli command in terminal which is command-line client for NetworkManager. It will show you security types of nearby Wi-Fi access points. Enter the following command in terminal:

It will show you the output like this:
Using the above methods, you should have known the encryption-type of targeted WiFi network which you want to hack. So, I am gonna show you how to hack WiFi Network for each of WEP, WPA and WPA2 PSK secured WiFi networks.
Requirements for Hacking WiFi Netwoks

My methods require KALI Linux which is especially designed Linux distrbution for penetration testing and ethical hacking. You can download it for free from its official site. Download Kali Linux ISO from its website either install it as separate operating system in your system or you can use Virtual Machine/VMware to directly run KALI Linux inside Windows.
You will also need Aircrack-ng which is a security suite to assess WiFi network security. It focuses on different area of WiFi security: monitoring, attacking, testing and cracking.
Another important requirement is to check if your wireless card is compatible with Aircrack-ng or not. Because if it’s not compatible, you need to have an Aircrack-ng compatible card. Check it directly here: http://www.aircrack-ng.org/doku.php or run aireplay-ng -9 mon0 command inside terminal to view the percentage of injection your card can do.
Install Aircrack-ng using the following command in KALI LINUX
- sudo apt-cache search aircrack-ng (to seach aircrack-ng or any related repositories)
- sudo apt-get install aircrack-ng (to install aircrack-ng repository)
Fulfill only these requirements and you are ready to hack any WiFi network, whether it is a WEP, WPA or WPA2 PSK Wi-Fi.
Steps to hack WiFi Networks
Starting below, I’ll be guiding you step-by-step in hacking a secured WiFi network. You can either scroll down to read each and every WiFi hacking method or can directly jump to the required section below using these links:
There are various methods to hack into WiFi network and crack its password for all the above security-types but I am showing only those methods with which I’ve had success in cracking password of desired WiFi network and hack secured WiFi Access points. So, if you follow these steps correctly, you’ll also be able to hack any WiFi hotspot available in your reach.
How To Hack WEP WiFi Network
In this method, we are going to hack WEP secured WiFi network using packet injection method inside KALI Linux operating system. So, start KALI Linux in your system. Now follow these below steps:
Step 1: Check Wireless Interface
- Open terminal in Kali Linux and enter the command airmon-ng. It will show you what network interface are you using. In my system, I have only one network interface card wlan0, which is my wireless interface card.
- Create a network interface which runs in monitor mode. To do this enter command airmon-ng start wlan0.Make sure to replace wlan0 in command with the interface name that your card have. Here, mon0 has been created.
- Now, you might or might not get the warning appearing in the below screenshot which tells other processes using the network which can create the problem. So, you can kill them using the syntax: kill PID if you know those processes are not important for you at the moment.
Step 2: Scan available WEP WiFi networks
- Now, enter the command airodump-ng mon0 to scan & list down all the available WiFi networks using created monitor interface (mon0). It can take time to all the available WiFi networks in range.
- Once the process is done,all the available WiFi access points will appear with their important details: BSSID (WiFi Access Point MAC Address), PWR (Signal strength value; the lower, the better), CH (Channel for WiFi), ENC (Encryption type), AUTH, ESSID (Name of WiFi)
- Select the WiFi network with WEP Encryption (ENC) and lowest PWR value.
Step 3: Attack the selected WEP WiFi Network
- Open another terminal concurrently and enter command: aidodump-ng -c 1 -w bell –bssid 64:0F:28:6B:A9:B1 mon0. Here, -c 1 indicates channel number which is 1, -w bell is to write data in file “bell”, –bssid 64:0F:28:6B:A9:B1 is MAC address for my selected WiFi access point and mon0 is monitor interface that was created above. Hit Enter and it will start sending packets (visible in #Data) to the WiFi
- The speed of sending data is very slow but you need to escalate it by attacking the WEP WiFi network. First enter the command airplay-ng -1 0 -a 64:0F:28:6B:A9:B1 mon0 to perform fake authentication (-1 in command) to the network.
- Now we will perform ARP REPLAY Attack to the WiFi network to climb the data to the network at enormous rate. Useairplay-ng -3 -b 64:0F:28:6B:A9:B1 mon0, where -3 is for ARP REPLAY attack. Hit enter and the command will start doing attack to WEP WiFi Access point and you can see the #Data value increasing at enormously fast rate.
- In below screenshot the bell-01.cap is the file where data is being stored that we will use to crack the password of this WEP WiFi network once we have enough data (recommended #Data value should be over 35,000).
- Once you have enough data in the file bell-01.cap, run the command aircrack-ng bell-01.cap. It will test all the data values available in key file and automatically show you the key it found by testing data in file.
- You can see in above screenshot that we have successfully cracked the password of targeted WEP WiFi network
- The key found will not be in those text or alphanumeric format that the WiFi owner has created. It will be in hex format but work just fine.
- Now, to use this key, firstly start the processes you have killed in Step 1 above using the command I have used below.
- Finally enter the cracked key 61:32:58:94:98 (without colon) as the password of targeted WEP WiFi Network and it will be connected.
Steps to Hack WPA/WPA2 Secured WiFi Network
Hacking into WPA/WPA2 WiFi Network is very tough, time & resource consuming. The technique used to crack WPA/WPA2 WiFi password is 4-way handshake for which there is a requirement to have at least one device connected to the network.
In WPA/WPA2 security method, the allowed password can have both large and small alphabets, numbers and symbols. And, allowed size of password is 64 characters. On a rough guess, if we consider password to be only 8 characters long and eliminate the use of symbols even then if you want to crack WPA or WPA2 WiFi password, using the brute force method the password combinations will be: 826+26+10=62 which is equals to:
- 98079714615416886934934209737619787751599303819750539264
So, even in fastest computer you can manage to use, it’s going to take hours.
Aircrack-ng have all the tools required to crack into WPA/WPA2 PSK WiFi network. It can perform 4-way handshake by disconnecting/connecting the connected device and capturing WPA handshake. It can perform brute-force attack but you can’t hope to crack the password if you have wordlist/dictionary for the password (which is already too big in size) with password inside it. I hate to tell you this but yes, doing it on your own can take forever.
However, there is a tricky way to crack WPA/WPA2 WiFi Password quickly which only requires you to be a bit lucky. The tool is fluxion. Fluxion use same 4-way handshake technique to crack secured WPA/WPA2 WiFi access points password but it doesn’t require you to have dictionary or perform brute force attack. So yes, it’s going to minimize your time to hack WPA or WPA2 WiFi networks password multiple folds.
Instead of doing this, it performs a little bit of phishing where the already connected user is asked to enter password of WiFi network again for security reason and when the user enter the password, first the handshake is checked with the earlier captured handshake of the device, if handshake is correct that means the password entered by user is correct. Once it is successful, Fluxion returns the key required to authenticate the network.
Steps to crack WPA/WPA2 WiFi Password using Fluxion
- Scan the networks.
- Capture a handshake (can’t be used without a valid handshake, it’s necessary to verify the password)
- Use WEB Interface *
- Launch a FakeAP instance to imitate the original access point
- Spawns a MDK3 process, which deauthenticates all users connected to the target network, so they can be lured to connect to the FakeAP and enter the WPA password.
- A fake DNS server is launched in order to capture all DNS requests and redirect them to the host running the script
- A captive portal is launched in order to serve a page, which prompts the user to enter their WPA password
- Each submitted password is verified by the handshake captured earlier
- The attack will automatically terminate, as soon as a correct password is submitted
I can understand that not all readers will be able to implement the method after reading such summarized version on hacking WPA/WPA2 PSK WiFi Network. So, below is the video tutorial on cracking WPA2 WiFi Access Point password using Fluxion.
https://youtu.be/4XLUVfoJqo8
Comments below if you face any problem in hacking WEP, WPA and WPA2 PSK WiFi Networks using the above methods.
Must Read –How To Hack a Website using SQL Injection
